screens: add screenshots to ESP/Jnouner_Router/README.md
This commit is contained in:
parent
d7a6234a60
commit
25a748043c
@ -58,7 +58,9 @@ a custom UDP protocol (JMP) to exfiltrate the final flag.
|
||||
|
||||
## Solution
|
||||
|
||||
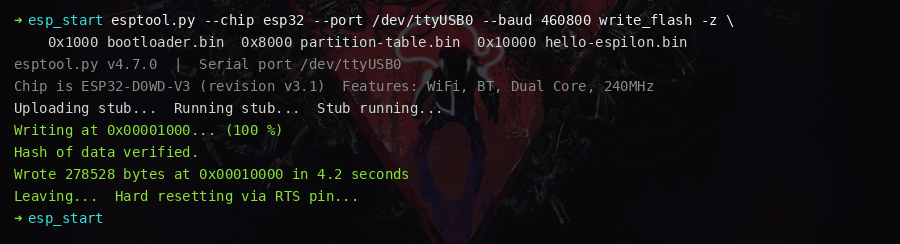
### Setup — Flash the firmware
|
||||
### Setup
|
||||
|
||||
— Flash the firmware
|
||||
|
||||
```bash
|
||||
esptool.py --chip esp32 --port /dev/ttyUSB0 --baud 460800 write_flash -z \
|
||||
@ -77,7 +79,9 @@ screen /dev/ttyUSB0 115200
|
||||
|
||||
---
|
||||
|
||||
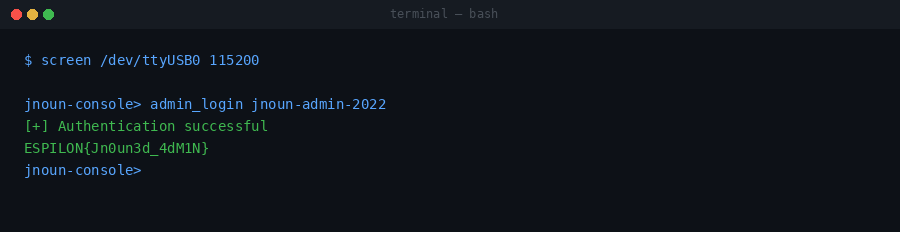
### Flag 1 — Console Access (100 pts)
|
||||
### Flag 1 — Console Access
|
||||
|
||||
(100 pts)
|
||||
|
||||
The UART console presents a `jnoun-console>` prompt requiring a password.
|
||||
|
||||
@ -101,7 +105,9 @@ Flag 1 is printed on success.
|
||||
|
||||
---
|
||||
|
||||
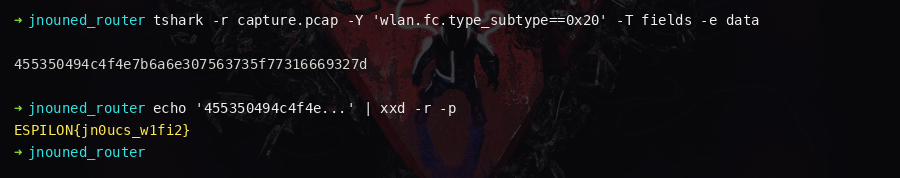
### Flag 2 — 802.11 TX (200 pts)
|
||||
### Flag 2 — 802.11 TX
|
||||
|
||||
(200 pts)
|
||||
|
||||
From the admin console, read device settings:
|
||||
|
||||
|
||||
Loading…
Reference in New Issue
Block a user